Towards Autonomous and Proactive Security in Software-Defined Edge Networks with Artificial Agents
DOI:
https://doi.org/10.64060/ICPP.03Keywords:
Research Proposal, Proactive Security, Autonomous Security, Artificial Agents, Software-Defined Edge NetworksAbstract
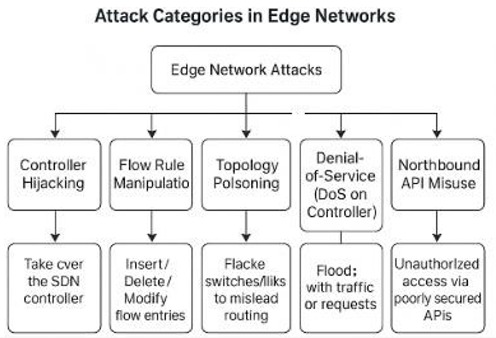
Edge computing is transforming latency‑sensitive systems such as autonomous vehicles, Industrial IoT, and smart infrastructure. Yet, when managed by centralized Software‑Defined Networking (SDN) controllers, these environments face complex security risks. Existing defenses are largely reactive, acting only after damage occurs. This research introduces a proactive, multi- agent AI security framework in which distributed agents monitor system status, detect anomalies, and recommend real-time policy adjustments. A novel coordination mechanism enables adaptive reconfiguration of SDN policies through programmable APIs. To address resource limitations at the edge, the framework employs federated learning and lightweight, self-optimizing models, delivering efficient and scalable security for resource-constrained environments. Prototyped on open‑source platforms and tested against real‑world attack scenarios, the framework will be evaluated for detection latency, resilience, and response efficiency. The evaluation should show that the framework provides a scalable, context-aware defense that strengthens the resilience of critical infrastructure in heterogeneous domains such as smart cities, healthcare, and energy.
Downloads
References
[1] W. Z. Khan, E. Ahmed, S. Hakak, I. Yaqoob, and A. Ahmed, “Edge computing: A survey,” Futur. Gener. Comput. Syst., vol. 97, pp. 219–235, 2019, doi: 10.1016/j.future.2019.02.050.
[2] N. Abbas, Y. Zhang, A. Taherkordi, and T. Skeie, “Mobile Edge Computing: A Survey,” IEEE Internet Things J., vol. 5, no. 1, pp. 450–465, 2018, doi: 10.1109/JIOT.2017.2750180.
[3] X. Zhang, C. Chen, Y. Xie, X. Chen, J. Zhang, and Y. Xiang, “A survey on privacy inference attacks and defenses in cloud-based Deep Neural Network,” Comput. Stand. Interfaces, vol. 83, p. 103672, 2023, doi: https://doi.org/10.1016/j.csi.2022.103672.
[4] D. Kreutz, F. M. V. Ramos, P. E. Verissimo, C. E. Rothenberg, S. Azodolmolky, and S. Uhlig, “Software-defined networking: A comprehensive survey,” Proc. IEEE, vol. 103, no. 1, pp. 14–76, 2015, doi: 10.1109/JPROC.2014.2371999.
[5] A. Hamarsheh, “An Adaptive Security Framework for Internet of Things Networks Leveraging SDN and Machine Learning,” Appl. Sci., vol. 14, no. 11, 2024, doi: 10.3390/app14114530.
[6] M. Raza, M. Jasim Saeed, M. B. Riaz, and M. Awais Sattar, “Federated Learning for Privacy-Preserving Intrusion Detection in Software-Defined Networks,” IEEE Access, vol. 12, no. May, pp. 69551–69567, 2024, doi: 10.1109/ACCESS.2024.3395997.
[7] A. A. Okon, “A Blockchain-enabled SDN Framework for Multi-operator Networks,” no. January, 2025.
[8] J. Chen, Q. Li, H. Wang, and M. Deng, “A machine learning ensemble approach based on random forest and radial basis function neural network for risk evaluation of regional flood disaster: A case study of the yangtze river delta, China,” Int. J. Environ. Res. Public Health, vol. 17, no. 1, pp. 1–21, 2020, doi: 10.3390/ijerph17010049.
[9] A. Rahdari et al., “Security and Privacy Challenges in SDN-Enabled IoT Systems: Causes, Proposed Solutions, and Future Directions,” Comput. Mater. Contin., vol. 80, no. 2, pp. 2511–2533, 2024, doi: 10.32604/cmc.2024.052994.
[10] J. C. Correa Chica, J. C. Imbachi, and J. F. Botero Vega, “Security in SDN: A comprehensive survey,” J. Netw. Comput. Appl., vol. 159, no. November 2019, p. 102595, 2020, doi: 10.1016/j.jnca.2020.102595.
[11] M. Abdallah, N. An Le Khac, H. Jahromi, and A. Delia Jurcut, “A Hybrid CNN-LSTM Based Approach for Anomaly Detection Systems in SDNs,” ACM Int. Conf. Proceeding Ser., 2021, doi: 10.1145/3465481.3469190.
[12] M. Mohammadi, A. Al-Fuqaha, S. Sorour, and M. Guizani, “Deep learning for IoT big data and streaming analytics: A survey,” IEEE Commun. Surv. Tutorials, vol. 20, no. 4, pp. 2923–2960, 2018, doi: 10.1109/COMST.2018.2844341.
[13] T. V. Phan, T. G. Nguyen, N. N. Dao, T. T. Huong, N. H. Thanh, and T. Bauschert, “DeepGuard: Efficient Anomaly Detection in SDN with Fine-Grained Traffic Flow Monitoring,” IEEE Trans. Netw. Serv. Manag., vol. 17, no. 3, pp. 1349–1362, 2020, doi: 10.1109/TNSM.2020.3004415.
[14] S. Ismail, S. Dandan, and A. Qushou, “Intrusion Detection in IoT and IIoT: Comparing Lightweight Machine Learning Techniques Using TON_IoT, WUSTL-IIOT-2021, and EdgeIIoTset Datasets,” IEEE Access, vol. 13, no. February, pp. 73468–73485, 2025, doi: 10.1109/ACCESS.2025.3554083.
[15] M. Rahouti, K. Xiong, Y. Xin, S. K. Jagatheesaperumal, M. Ayyash, and M. Shaheed, “SDN Security Review: Threat Taxonomy, Implications, and Open Challenges,” IEEE Access, vol. 10, no. April, pp. 45820–45854, 2022, doi: 10.1109/ACCESS.2022.3168972.
[16] K. M. Kokila M and S. R. K. Srinivasa Reddy Konda, “DeepSDN: Deep Learning Based Software Defined Network Model for Cyberthreat Detection in IoT Network,” ACM Trans. Internet Technol., 2025, doi: 10.1145/3737875.
[17] Y. Tseng, F. Naït‑ Abdesselam, and A. Khokhar, “A comprehensive 3‑ dimensional security analysis of a controller in software‑ defined networking,” Secur. Priv., vol. 1, no. 2, 2018, doi: 10.1002/spy2.21.
[18] A. Hirsi, L. Audah, A. Salh, M. A. Alhartomi, and S. Ahmed, “Detecting DDoS Threats Using Supervised Machine Learning for Traffic Classification in Software Defined Networking,” IEEE Access, vol. 12, no. September, pp. 166675–166702, 2024, doi: 10.1109/ACCESS.2024.3486034.
[19] Z. Chen, N. Lv, P. Liu, Y. Fang, K. Chen, and W. Pan, “Intrusion Detection for Wireless Edge Networks Based on Federated Learning,” IEEE Access, vol. 8, pp. 217463–217472, 2020, doi: 10.1109/ACCESS.2020.3041793.
[20] A. John, I. F. Bin Isnin, S. H. H. Madni, and M. Faheem, “Cluster-based wireless sensor network framework for denial-of-service attack detection based on variable selection ensemble machine learning algorithms,” Intell. Syst. with Appl., vol. 22, no. December 2023, p. 200381, 2024, doi: 10.1016/j.iswa.2024.200381.
[21] I. Akbari, E. Tahoun, M. A. Salahuddin, N. Limam, and R. Boutaba, “ATMoS: Autonomous Threat Mitigation in SDN using Reinforcement Learning,” Proc. IEEE/IFIP Netw. Oper. Manag. Symp. 2020 Manag. Age Softwarization Artif. Intell. NOMS 2020, 2020, doi: 10.1109/NOMS47738.2020.9110426.
[22] S. Facchinetti, S. A. Osmetti, and C. Tarantola, “Network models for cyber attacks evaluation,” Socioecon. Plann. Sci., vol. 87, no. PB, p. 101584, 2023, doi: 10.1016/j.seps.2023.101584.
[23] A. M. Sheikh, M. R. Islam, M. H. Habaebi, S. A. Zabidi, A. R. Bin Najeeb, and A. Kabbani, “A Survey on Edge Computing (EC) Security Challenges: Classification, Threats, and Mitigation Strategies,” Futur. Internet, vol. 17, no. 4, pp. 1–54, 2025, doi: 10.3390/fi17040175.
[24] I. Sharafaldin, A. H. Lashkari, and A. A. Ghorbani, “CICIDS2017: Intrusion Detection Evaluation Dataset,” pp. 1–11, 2017.
[25] I. Sharafaldin, A. Habibi Lashkari, and A. A. Ghorbani, “A Detailed Analysis of the CICIDS2017 Data Set BT - Information Systems Security and Privacy,” P. Mori, S. Furnell, and O. Camp, Eds., Cham: Springer International Publishing, 2019, pp. 172–188.
[26] N. Moustafa, “A new distributed architecture for evaluating AI-based security systems at the edge: Network TON_IoT datasets,” Sustain. Cities Soc., vol. 72, p. 102994, 2021, doi: 10.1016/j.scs.2021.102994.
[27] A. Azab, M. Khasawneh, S. Alrabaee, K. K. R. Choo, and M. Sarsour, “Network traffic classification: Techniques, datasets, and challenges,” Digit. Commun. Networks, vol. 10, no. 3, pp. 676–692, 2024, doi: 10.1016/j.dcan.2022.09.009.
Downloads
Published
Issue
Section
License
Copyright (c) 2026 Fatima Abbas , Muhammad Anas Khalid , Awais Rasool (Author)

This work is licensed under a Creative Commons Attribution 4.0 International License.








